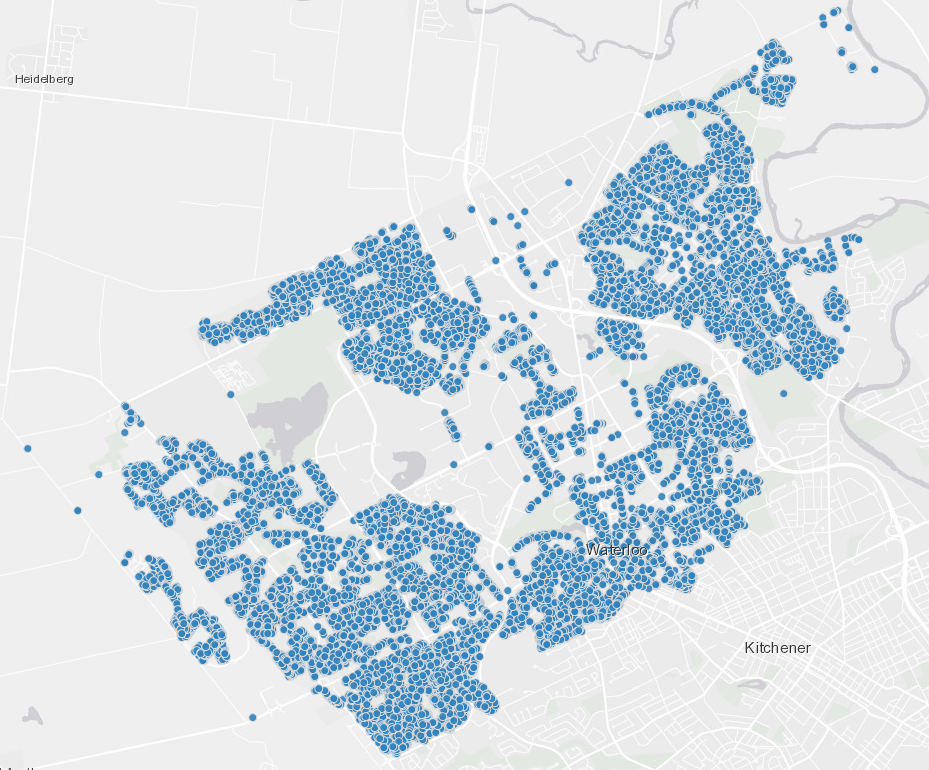
Can We Trust Marathon Pacers?
A pacer is an experienced runner that commits to other runners to run a race or a section of it in a predefined duration or speed. They also help with mental support for those who are struggling to stay out of their comfort zone. Many races have pacers, but not all. The ones that have attracted many runners looking for some help with their personal goals, like getting a new personal best, finishing a marathon under 4 hours, or even qualifying for Boston. But can we fully trust them to deliver what they committed to?
Continue reading...Introducing LibRunner
A good deal of being a geek is to code or understand coding. We love objectivity and hate subjectivity, so coding is the ultimate objectivity sophistication. If something can be expressed in numbers and logic, then code is the best way to materialize and document it. That’s why we created a programming library where we can express all the calculations related to running and let other geeks use and contribute to it.
Continue reading...Clojure Books in the Toronto Public Library

8 years ago I failed to write a book. I wrote it until chapter 3 but I couldn’t stand all the criticism coming from the editor and the reviewers. As the deadline to deliver chapter 4 was approaching, I was still overwhelmed by all the work to catch up with their feedback. So, I quit, but I learned something very important from that experience: the scrutiny over the writing of books makes them very good references.
Continue reading...Once Upon a Time in Russia

I was a Ph.D candidate in 2009, in the Electrical Engineering department, at Université catholique de Louvain. A coleague of mine, Russian, told me about this conference in Saint Petersburg and asked me if I wanted to submit a paper. I agreed, we wrote it together and it got accepted. Since she was in Moscow at the time, I thought she would present the paper, but our lab had a policy that they could only pay for trips from Belgium to Russia, not from Russia to Russia. So, I had to go.
Continue reading...